The following instructions will show you how to create a rule in Exchange 2016 or Microsoft 365 that will prevent your domain from being spoofed from outside your environment. However, this rule will not prevent a person from sending someone else outside your organization an email that looks like it comes from your organization.
This rule will accomplish the following:
- Delete any inbound emails that originate from outside your organization which appear as if they are coming from your domain or inside your organization.
- Allow emails from KnowBe4’s servers to bypass this rule so phishing tests can be conducted that look like they are coming from internal email accounts.
Creating the New Rule
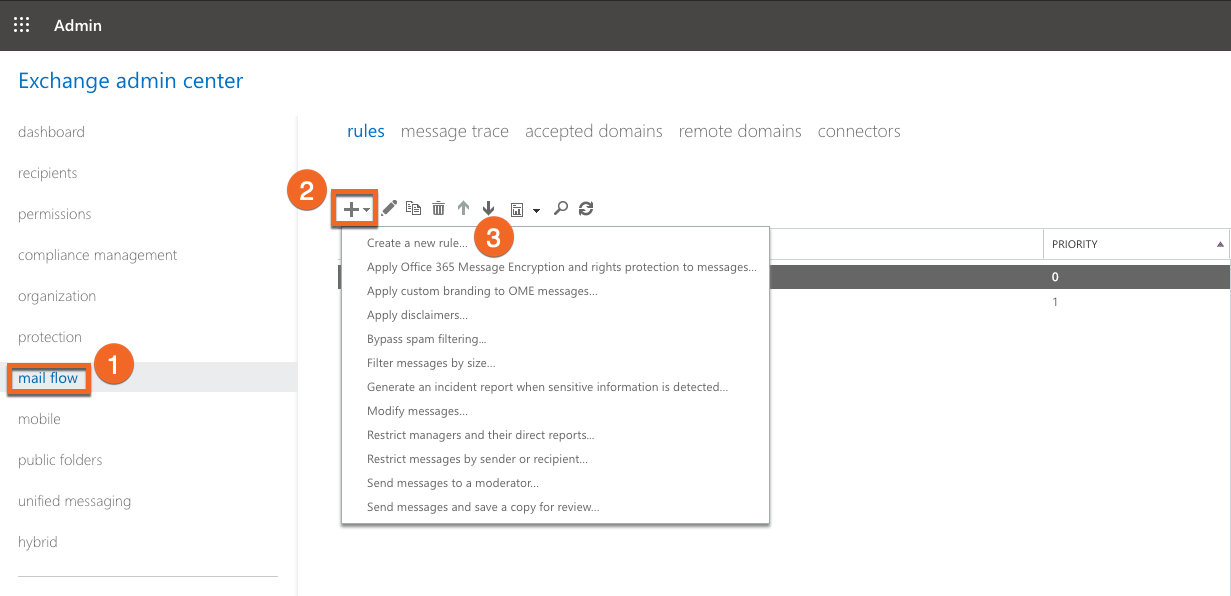
The below screenshots display a Microsoft 365 environment.
- Log in to your Exchange or Microsoft 365 portal and go into the Admin> Exchange area.

- Click on the mail flow section and then click the + sign in the right-hand area and select Create a new rule…
- Give the rule a relevant name, such as Domain Spoof Prevention and then click on more options.
- Select Apply this rule if… and then The sender is internal/external. Select the location to outside the organization.
- Add a condition and then choose The sender's domain is and input your organization’s email domain(s).
- Choose a reaction based on your security policies. If you would like to automatically delete messages which spoof your domain, choose Block the message then delete the message without notifying anyone.
- Add an exception for KnowBe4 or any other external organization that may need to send an email as if it is coming from your domain to your users.
- Choose Sender’s IP address is in any of these ranges or exactly matches… and fill in the IP Addresses of the external organization’s mail server.
Note: For the most up-to-date list of our IP addresses, please see this article. For more Whitelisting information, please see this article.
- Under Match sender address in message and select Header or envelope.

- Be sure to save your new rule once all settings match.
How Do I Remove Domain Sender Permissions
If you are using Exchange 2010, you have the option of removing your domain sender permissions. These permissions will remove the possibility of receiving spam from outside of your organization that appears to come from inside of your domain. To learn how to remove these permissions, please see the Remove domain sender permissions Exchange 2010 article.